Fortinet
Fortinet's Fortigate-based Secure SD-WAN solution provides next-generation security and networking capabilities to improve WAN efficiency without sacrificing security.
Adoption of cloud services is critical to mobile workforce next-generation security strategies, with multipath WAN accelerating the advancement in WAN technologies.
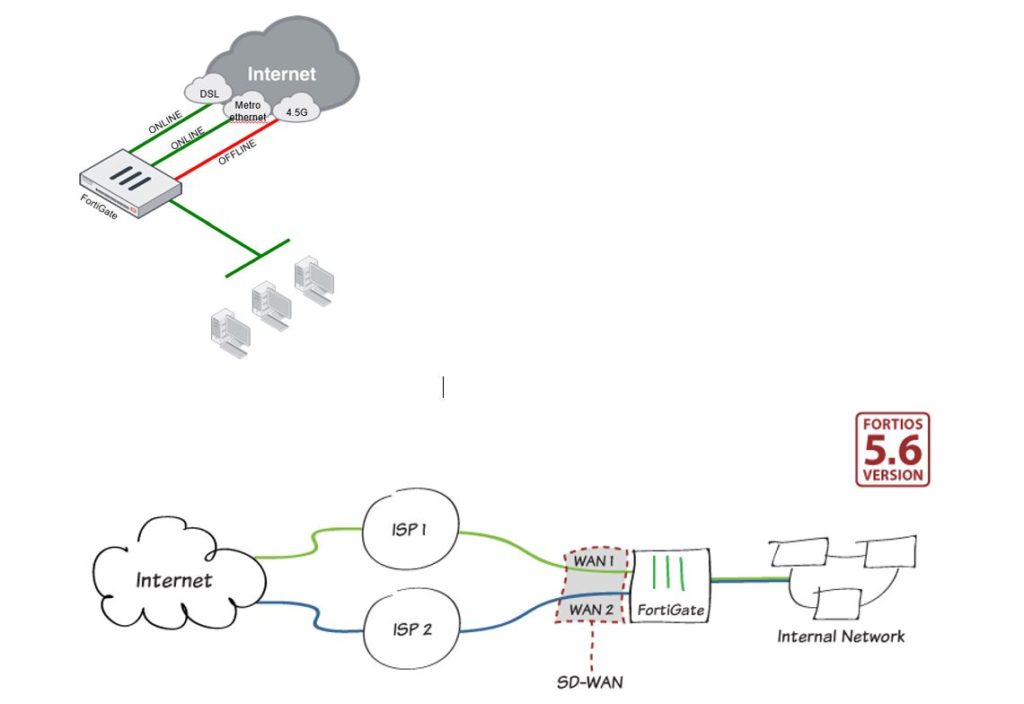
Load-balancing between multiple WAN lines, especially in distributed organizations (for example, active/active use of two ADSL lines at the same time). Making status checks of each WAN line and routing all traffic to the other WAN line in case the line slows down becomes very valuable issues.
Security Fabric
The Fortinet Security Fabric platform provides true integration and automation throughout an organization's security infrastructure, offering unmatched protection and visibility for every network segment, device, and device in the virtual, cloud, or on-premises environment.
Firewall solutions
 Fonetsan provides 24/7 network security service to its customers with its certified engineer team.
Fonetsan provides 24/7 network security service to its customers with its certified engineer team.
Firewall solutions targeting small and large businesses consist of software or hardware components. Software solutions only protect installed computers. To protect all computers on the network, software must be installed on each of them individually. Managing these software is both expensive and difficult to manage.
Hardware-based firewall solutions protect all computers on your network. Hardware-based firewalls are easy to manage.
In addition, these firewall solutions come with a comprehensive security suite that includes virtual private network (VPN) support, antivirus, antispam, antispyware and content filtering capabilities.
Operating in the province of Izmir, Fonetsan is at your service with your fortinet firewall requests, especially in the Aegean Region and all over Turkey. You can contact us for all your questions and problems.
| Firewall | Powerful complete content inspection firewall; It offers maximum performance and scalability. Firewalls generally protect internal computer networks from dangerous external access, however, Firewalls can also be configured to restrict external access from internal computers. Fortinet's FortiASIC chip enhances the firewall capabilities of FortiGate systems, enabling gigabit performance for inline network deployment. |
| Antivirus | Detects and removes viruses, worms and spyware in real time. Scans all FTP and HTTP traffic, including inbound and outbound email attachments (SMTP, POP3, IMAP) and web-based emails, without reducing performance. Antivirus gateway closes the gap by stopping viruses and worms before they enter the network. Fortinet's worldwide antivirus staff work 24x7 and provide continuous virus signature updates to its customer base using the global FortiGuard Distribution Network. As verified by independent organization AVTest.org, Fortinet has repeatedly been one of the first and fastest to develop antivirus definitions for new threats. Fortinet systems are updated instantly through the FortiGuard Distribution Network. |
| AntiSpam | It has the capability of blacklisting websites and internet domains, keyword scanning of emails (each can be configured per user in the FortiMail system), and a dynamic scoring system using multiple criteria (FortiMail). FortiGuard Antispam updates have blacklist and whitelist support. FortiGuard Antispam Service; Enhances existing Real-Time RBL List (RBL – Real-Time Blackhole List) capability by providing a two-stage spam detection method. In addition to checking the spammer's IP address, FortiGuard Antispam Service maintains a list of links in the spam mail. FortiGuard Antispam Service uses Fortinet's spam probes (spam sensors) located in different parts of the world to detect spam mails. This constantly updated information enables to build sensitive spammer lists and increase spam detection rate. Fortinet's FortiMail Systems use FortiGuard Antispam service with enterprise antispam and antivirus features to secure critical email applications. Built on Fortinet's unique and award-winning FortiOS and FortiASIC technology, FortiMail antivirus technology has full content inspection capabilities to detect the most advanced email threats. |
| Intrusion Detection | It has more than 4,000 known attack signatures. FortiGate Multi-Threat Security Systems stop attacks that evade ordinary antivirus protection with a real-time response to rapidly spreading threats. Fortinet's worldwide IPS engineering team works 24/7 and provides real-time attack signatures to the Fortinet customer base. FortiOS; Using the global FortiGuard Distribution Network, it stops the most dangerous attacks on network connections, regardless of whether the network is wired, wireless, partner extranet, or branch office networking. Fortinet technology also; It offers behavior-based heuristic recognition capabilities beyond simply matching content with known definitions. |
| Web Filtering | Scans all web content for known dangerous URLs to prevent inappropriate content and dangerous scripts from entering the network, including Java Applets, Cookies and ActiveX scripts. With FortiGuard services, users can manually enter additional URL definitions on their FortiGate system. Web content filtering provides increased efficiency in companies and institutions, and protects children from harmful content of the Internet in educational institutions. |
| VPN | It provides industry-based IPSec, SSL-VPN, PPTP and L2TP-based VPN support and creates secure communication tunnels between clients. Fortinet's ASIC accelerated VPN capabilities; It enables institutions to exchange information securely over the internet. FortiClient VPN; authenticates users, encrypts data and otherwise manages sessions. FortiGate system VPNs reduce network connection costs compared to alternatives such as traditional leased lines or remote access servers. |
| Traffic Control | Fortinet's traffic shaping function allows users to control network traffic to optimize network traffic, avoid delays and provide high performance. FortiOS operating system; It provides packet classification and sequencing, rule enforcement, quality of service (QoS) and compliance with rules. Because network bandwidth is a limited resource, traffic shaping helps businesses prioritize and manage costly network services. Traffic shaping, when managed intelligently; It helps to increase efficiency on the network. |
| Application Control | Application control technology is a set of rules that aim to control the application-based traffic of users on the network. Thanks to this technology, FortiGate devices can dynamically detect application signature and/or protocol information in traffic. Many web-based applications contain threats and harmful content. The application control mechanism has an infrastructure to stop both threatening and potentially dangerous applications, depending on the traffic behavior and the features it contains. |
| Data Exfiltration | The DLP system is designed to detect and prevent the distribution of a data or data set that does not comply with company policies and rules. It can detect and stop the content information in various applications with the FortiOS system. The source that wants to distribute can be determined with this system and restricted for a certain period of time within the framework of the desired rules. |
| WAN Optimization | WAN Optimization application can be used on FortiGate devices that contain HDD or can be installed HDD. The purpose of the system is to use less bandwidth and be faster by compressing the data transfer in the communication on the wide network or point-to-point connections. As a result, it is aimed to reduce data privacy, security, high performance transmission and line cost. |
| SSL Control | In this technology, SSL content is controlled by FortiOS and data security is ensured. Malware can be detected by terminating SSL traffic in the FortiGate system. Otherwise, since the SSL content will be confidential and protected, data control will not be possible. |
 ]
]